August 12th, 2021
Active Directory Audit
Why Active Directory Audits should be an important component of your information security program
Security appliances such as Tenable’s Nessus and Qualys assist with scanning an organization’s assets for misconfigurations, security vulnerabilities, and missing patches – however, they ignore a very big culprit for risks within a Windows environment: Active Directory.
Active Directory (AD) handles all the Windows Domain-based authentication and authorization, as well as assigning and enforcing security policies via Group Policy Objects (GPOs). Attackers can abuse misconfigurations within an organization’s AD to operate under the radar, move laterally, and escalate privileges.
Auditing the AD environment can help detect these issues and limit the security risks to the Windows Domain. The audit reports provide a detailed explanation of each finding as well as steps to mitigate and approach full remediation. A robust AD infrastructure can greatly increase the efficiency of both the IT staff and Blue Team defenders and reduce attack paths while identifying areas for growth.
BloodHound
BloodHound is an open-source project developed and maintained by SpecterOps. Its main components focus on the visualization of AD attributes and analyzing the relationships; however, it also includes “Ingestors” which perform the collection and formatting of data from a Domain Controller.
Collection Methods
SharpHound
SharpHound is one of the BloodHound Ingestors included within the repository. The Github repo has both a Windows executable version and a Powershell script version. Many Anti-virus/EDR products will detect/block these tools due to their usage by attackers, however they can still be used for defensive purposes to identify areas of risk. SharpHound will need to run on a Windows machine with valid credentials to the targeted Windows Domain.
BloodHound.py
BloodHound.py is an open-source product developed by Fox-IT. The Github repo has some limitations compared to the BloodHound v4 Ingestors but is a great resource as it can be run from a non-Domain joined Linux machine. It utilizes Python3 libraries to perform all the necessary LDAP queries to gather the information from the Domain into a format acceptable by the BloodHound UI.
Visualization
All of the extracted JSON files contain the LDAP attributes pulled from the Active Directory instance on the Domain Controller. By importing them into the BloodHound UI, a graphical representation of the AD environment allows for attack path mapping, relationship management, and attack strategies.
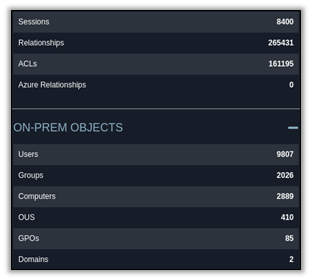
Figure 1: BloodHound Database Statistics
Group Membership
Clients commonly do not know how many privileges accounts exist in their Domain environment. “How many Domain Admins does your organization have?” is often answered with “We have X IT personnel”, which doesn’t take into account the other elevated users or service accounts likely present.
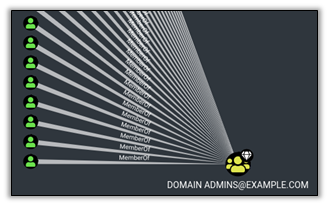
Figure 2: Members of the Domain Admins Group
User Path Mapping
BloodHound allows you to configure the settings for each node, which consist of Users, Computers, Domains, GPOs, etc. Nodes can be set as starting or ending nodes to discover paths to or from an object based on the relationships and Access Control Lists (ACLs) within the domain. The UI also allows changing properties about a node, such as the name, marking it as “owned”, or as a High Value Target (HVT). The HVT property is used in other BloodHound queries to describe paths to get to valuable nodes.
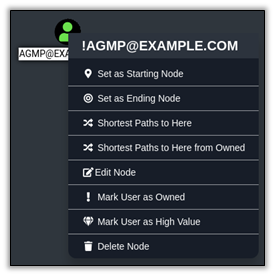
Figure 3: Node Properties and Path Options
Lateral Movement
Each node’s attributes describe how it relates to other nodes within the domain. These links are drawn within the BloodHound UI to visualize lateral movement potentials based on privileges and permissions. These links can show things such as: RDP, PS-Remoting, Execute DCOM, SQL Admin, Local Admin, etc. Focusing on these traits can help discover ways to traverse the network and find a specific goal, such as an HVT or Domain Admin.
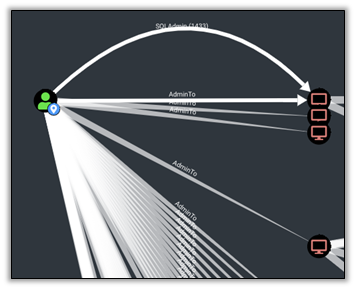
Figure 4: Lateral Movement Links
Attack Strategies
Each link within the BloodHound UI provides additional details for how that link could be used/abused to move laterally or escalate privileges within the environment. These help menus can be invaluable and save time when trying to utilize a target’s attributes.
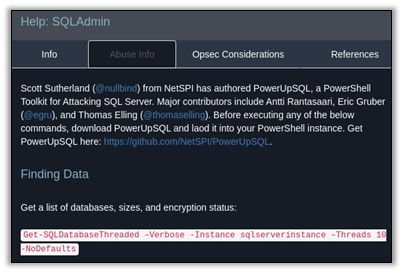
Figure 5: Lateral Movement Link’s Help Menu
Most Common AD Findings
During the numerous Active Directory audits PLEX Cyber has performed, there are common trends in the shortcomings and vulnerabilities present in the AD structure.
LAPS Not Deployed
Domain Admin accounts have extremely powerful permissions within a domain, making them a high-value target to attackers. With DA privileges, the domain is considered to be completely compromised and can often lead to the compromise of other trusted domains.
Any time a logon session is granted to a computer, that account’s authentication information exists in memory. If an attacker can compromise a machine with a DA’s token in memory, they can impersonate that DA and hijack their permissions over the domain. Because of this, DAs should only be used to log onto Domain Controllers and perform their administrative functions there.
If a DA needs to administrate a non-DC machine, they should utilize a Microsoft technology called Local Admin Password Solution — LAPS. LAPS will allow local admin access to any LAPS-configured machine with a unique local admin password per machine. This highly restricts attackers from performing lateral movement within the domain and helps to eliminate DA tokens on non-DC systems.
Because of the unique local admin passwords, if a machine is compromised, they cannot use the password or hash of the local admin’s account to pivot to other machines. Below shows an example of Domain Admin sessions on non-DC systems and shows the risk exposure of DA credentials since LAPS was not utilized properly.
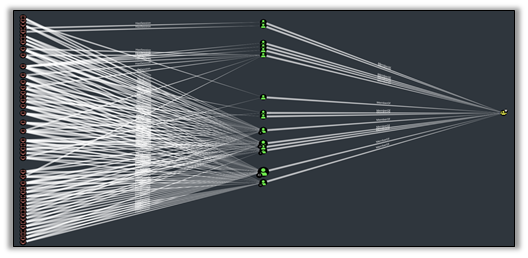
Figure 6: Domain Admin Sessions on Non-Domain Controllers
Kerberoasting
Domain accounts with a Service Principal Name (SPN) set are susceptible to an attack called “Kerberoasting”. SPNs are assigned to accounts that run services within the domain environment, often related to service accounts. When a user requests access to a service, they receive a Kerberos ticket cryptographically signed with the associated account’s NTLM hash. Kerberoasting is the process of requesting and exporting these signed tickets, with the goal of performing offline brute force attacks to derive the service account’s password. If the password is compromised, the service account can be impersonated within the domain, allowing the attacker to inherit all associated permissions and privileges of the service account.

Figure 7: User Relationship to HVT Group
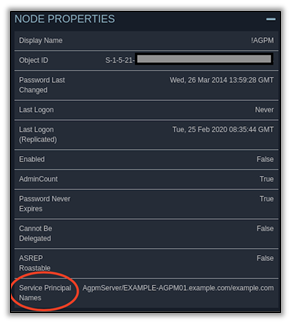
Figure 8: Service Principal Name Attribute
SMB Signing Disabled
SMB Signing is an improvement to the NTLM authentication mechanism used by Windows services and accounts. SMB Signing uses cryptographic protections to disable NTLM-Relaying attacks by ensuring the source and destination of authentication remains unchanged. Without SMB Signing, a malicious network user may abuse ARP poisoning techniques to hijack NTLM authentication traffic to gain access to resources without any passwords or hashes needed.
SMB Signing can be enforced with a simple GPO.
Excessive Admin Privileges
Any user with Local Admin privileges can fully control a system. Local Admins can elevate their access to the “NT AUTHORITY/SYSTEM” level, which is able to compromise account credentials from memory. Domain accounts compromised could allow lateral movement within the domain or full domain compromise.
If a user with Local Admin privileges falls victim to a phishing attack, the attacker can abuse those permissions to harvest credentials from the related systems in the domain. As such, users and groups should be audited for their Local Admin privileges and limited to reduce risk exposure.
Conclusion
Active Directory is a dynamic resource that changes constantly due to account and privilege changes. Monitoring these changes and auditing the AD structure helps detect flaws that could be abused by attackers and assists the IT personnel to secure the environment. PLEX Cyber is well versed in performing AD audits and is available to assist.
For more information on how PLEX Cyber can help your organization secure its AD environment, please contact Christina Majernik, VP at christina.majernik@plex-llc.com
