Continuous advantages to continuous security testing
Posted in: Cyber News Uncategorized
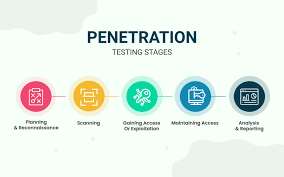
Continuous testing is a method of testing software in which testing is performed regularly and consistently throughout the development process. This approach is superior to a single penetration test, which is a one-time evaluation of a system’s security, because it…
4 Ways To Improve Your Cybersecurity Budget This Year
Posted in: Cyber News Uncategorized
Joe Petre – Vice President – PLEX Cyber Penetration testing is a valuable tool for demonstrating the need for security initiatives and budget to decision makers within an organization, too bad it’s often used to simply check a box for…
Adversaries are better at continuous improvement than you are.
It’s a bold statement, right? It’s true. I’ve spent the past 24 years in IT and security and most of that time was on the defense side working in MSS, enterprise security software, professional services, etc. With this experience, I now understand…
Stan Nolen to be Keynote Speaker for AUTOTESTCON!
Posted in: Cyber News Solutions Uncategorized
Stan began his career in the USAF as an enlisted Intelligence Analyst and was subsequently commissioned as a Cyber Warfare Officer. He served in various roles protecting and serving our country, including cyber, intelligence, ISR, electronic warfare, and Information Operations…
Washington Post 2022 Top Workplace!
Posted in: Cyber News Solutions Uncategorized
We are thrilled to announce that we have been recognized as a Washington Post 2022 Top Workplace! Thank you to our amazing employees who made this award possible! We are honored by this recognition and had a great time at…
HackASat3 Qualifiers
Posted in: Cyber News Solutions Uncategorized
For the third consecutive year, the combined team of CrypticVector (https://crypticvector.com/) and PLEX battled everything from orbital mechanics to telemetry to reverse engineering in a 30-hour competition! For the third consecutive year they claimed victory and finished in 5th place…
HackASat 3
Posted in: Cyber News Solutions Uncategorized
PLEX partnered with CrypticVector (https://crypticvector.com/) in an elite competition involving complex space physics, satellite communications challenges, reverse engineering, and hacking over the 21 May weekend.
Cybersecurity Association of Maryland (CAMI)
Posted in: Cyber News Solutions Uncategorized
A big PLEX thank you to Cybersecurity Association of Maryland, Inc. (CAMI) for hosting an incredible night of cocktails, laughs, and team building at their Chopped Mixology Event! The Ladies of PLEX showed up and represented! It was great to be able…
Password Audit
Posted in: Cyber
Why Password Audits need to be on your priority list ASAP. While many authentication mechanisms are adapting current technology trends such as Multi-Factor Authentication, Biometric sensors, and cryptographic tokens, there is one component that will remain prevalent for the foreseeable future – passwords. Passwords control the access to…
Nessus versus Penetration Test
Posted in: Cyber
Why Nessus Scans cannot replace Penetration Testing. Many organizations utilize security products to support their IT and Cybersecurity personnel. These applications can assist with Vulnerability Management, Asset Management, and Network Management, often incorporating features that give visibility and statistics on their findings within…
Post navigation
- 1
- 2